CVE-2026-23988
Rufus has Local Privilege Escalation via TOCTOU Race Condition in Fido Script Handling
Description
Rufus is a utility that helps format and create bootable USB flash drives. Versions 4.11 and below contain a race condition (TOCTOU) in src/net.c during the creation, validation, and execution of the Fido PowerShell script. Since Rufus runs with elevated privileges (Administrator) but writes the script to the %TEMP% directory (writeable by standard users) without locking the file, a local attacker can replace the legitimate script with a malicious one between the file write operation and the execution step. This allows arbitrary code execution with Administrator privileges. This issue has been fixed in version 4.12_BETA.
INFO
Published Date :
Jan. 22, 2026, 10:16 p.m.
Last Modified :
Feb. 27, 2026, 2:36 p.m.
Remotely Exploit :
No
Source :
[email protected]
CVSS Scores
| Score | Version | Severity | Vector | Exploitability Score | Impact Score | Source |
|---|---|---|---|---|---|---|
| CVSS 3.1 | HIGH | [email protected] | ||||
| CVSS 3.1 | HIGH | MITRE-CVE | ||||
| CVSS 3.1 | HIGH | [email protected] |
Solution
- Update Rufus to the latest version.
- Apply version 4.12 or newer.
- Avoid using versions 4.11 and below.
References to Advisories, Solutions, and Tools
Here, you will find a curated list of external links that provide in-depth
information, practical solutions, and valuable tools related to
CVE-2026-23988.
| URL | Resource |
|---|---|
| https://github.com/pbatard/rufus/commit/460cc5768aa45be07941b9e4ebc9bee02d282873 | Patch |
| https://github.com/pbatard/rufus/releases/tag/v4.12_BETA | Broken Link |
| https://github.com/pbatard/rufus/security/advisories/GHSA-hcx5-hrhj-xhq9 | Exploit Vendor Advisory |
CWE - Common Weakness Enumeration
While CVE identifies
specific instances of vulnerabilities, CWE categorizes the common flaws or
weaknesses that can lead to vulnerabilities. CVE-2026-23988 is
associated with the following CWEs:
Common Attack Pattern Enumeration and Classification (CAPEC)
Common Attack Pattern Enumeration and Classification
(CAPEC)
stores attack patterns, which are descriptions of the common attributes and
approaches employed by adversaries to exploit the CVE-2026-23988
weaknesses.
We scan GitHub repositories to detect new proof-of-concept exploits. Following list is a collection of public exploits and proof-of-concepts, which have been published on GitHub (sorted by the most recently updated).
Results are limited to the first 15 repositories due to potential performance issues.
The following list is the news that have been mention
CVE-2026-23988 vulnerability anywhere in the article.
-
Daily CyberSecurity
The Backup Backdoor: How a Simple File Edit Grants Full SYSTEM Control in IDrive for Windows
A critical local privilege escalation vulnerability has been discovered in the IDrive Cloud Backup Client for Windows, potentially allowing low-privileged users to seize full control of an affected ma ... Read more

-
Daily CyberSecurity
Booting Up Malware: Critical Flaw in Rufus Grants Admin Access (CVE-2026-23988)
A high-severity security flaw has been discovered in Rufus, the ubiquitous utility used by millions of IT professionals to format and create bootable USB drives. The vulnerability, tracked as CVE-2026 ... Read more
The following table lists the changes that have been made to the
CVE-2026-23988 vulnerability over time.
Vulnerability history details can be useful for understanding the evolution of a vulnerability, and for identifying the most recent changes that may impact the vulnerability's severity, exploitability, or other characteristics.
-
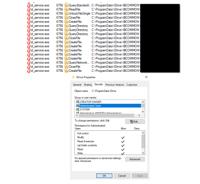
Initial Analysis by [email protected]
Feb. 27, 2026
Action Type Old Value New Value Added CVSS V3.1 AV:L/AC:H/PR:L/UI:N/S:U/C:H/I:H/A:H Added CPE Configuration OR *cpe:2.3:a:akeo:rufus:*:*:*:*:*:*:*:* versions up to (excluding) 4.12 Added Reference Type GitHub, Inc.: https://github.com/pbatard/rufus/commit/460cc5768aa45be07941b9e4ebc9bee02d282873 Types: Patch Added Reference Type GitHub, Inc.: https://github.com/pbatard/rufus/releases/tag/v4.12_BETA Types: Broken Link Added Reference Type GitHub, Inc.: https://github.com/pbatard/rufus/security/advisories/GHSA-hcx5-hrhj-xhq9 Types: Exploit, Vendor Advisory -
New CVE Received by [email protected]
Jan. 22, 2026
Action Type Old Value New Value Added Description Rufus is a utility that helps format and create bootable USB flash drives. Versions 4.11 and below contain a race condition (TOCTOU) in src/net.c during the creation, validation, and execution of the Fido PowerShell script. Since Rufus runs with elevated privileges (Administrator) but writes the script to the %TEMP% directory (writeable by standard users) without locking the file, a local attacker can replace the legitimate script with a malicious one between the file write operation and the execution step. This allows arbitrary code execution with Administrator privileges. This issue has been fixed in version 4.12_BETA. Added CVSS V3.1 AV:L/AC:L/PR:L/UI:R/S:U/C:H/I:H/A:H Added CWE CWE-367 Added Reference https://github.com/pbatard/rufus/commit/460cc5768aa45be07941b9e4ebc9bee02d282873 Added Reference https://github.com/pbatard/rufus/releases/tag/v4.12_BETA Added Reference https://github.com/pbatard/rufus/security/advisories/GHSA-hcx5-hrhj-xhq9